
“Infiltra.ai has become a security extension to our app team, helping us stay ahead of emerging threats.”
Infiltra.ai automates discovery, validates real impact with evidence, and retests fixes, reducing noise and giving teams a clear path to closure.
Traditional penetration testing is infrequent, expensive, and manual, struggling to keep pace with modern release cycles.
Many organizations lack dedicated security engineers with pentesting skills, creating gaps in vulnerability detection.
Legacy "automated" tools only identify simple CVEs; they cannot chain exploits or validate the real-world impact of a vulnerability.
Annual pentests are "health check-ups" that go stale the moment your next code commit goes live, creating massive risk gaps.
Manual testing involves slow RFP cycles and weeks of scheduling, making it impossible to scale at the pace of modern development.
Without automation, it’s hard to continuously assess fast-moving CI/CD environments.
Retesting after remediation is slow and expensive hence it gets skipped.
Infiltra.ai is an automated penetration testing platform built around specialised autonomous agents that replicate what an experienced pentester would do; discover attack surface, attempt exploitation, validate impact, and provide actionable remediation guidance.
Beyond basic crawling, our browser agents perform deep, authenticated testing by managing session states and complex user workflows just like a skilled pen tester.
Seamlessly ingest OpenAPI or Postman collections to map hidden endpoints, ensuring your entire backend attack surface is validated against real-world exploits.
Trigger assessments instantly, schedule recurring security checks, or integrate directly into your CI/CD pipeline via webhooks for true DevSecOps velocity.
Infiltra operates as a pure SaaS platform. There is no software to manage and no agents to install on your servers—allowing you to start scanning in under five minutes.
From configuration to validated exploits and tailored reporting in a single flow.
Create a scan config in 4 easy steps. Choose region and schedule. Upload OpenAPI/Postman collections for APIs.
Spider URLs and endpoints.
Browser agent can authenticate and
persist session state during the scan.
Specialised agents attempt exploits (e.g., file upload) and
validate impact.
WAF-aware payload crafting.
Persona based reporting with evidence.
Run delta scans
against
any full scan from the last 6 months.
Built for teams that want pentest-quality outcomes continuously, without manual overhead.
Agents test and confirm exploits. Findings include payloads and reproduction evidence when applicable.
Agents chain exploits when relevant (e.g., XSS → token theft → API access). Depth is objective driven.
Horizontal and vertical privilege escalation attempts after foothold, with re-scan from elevated context.
Browser agents with vision models can automate MFA/2FA scan configuration and handle UI-driven authentication steps.
During discovery/exploitation, responses are inspected for PII patterns and sensitive technical data (keys/creds).
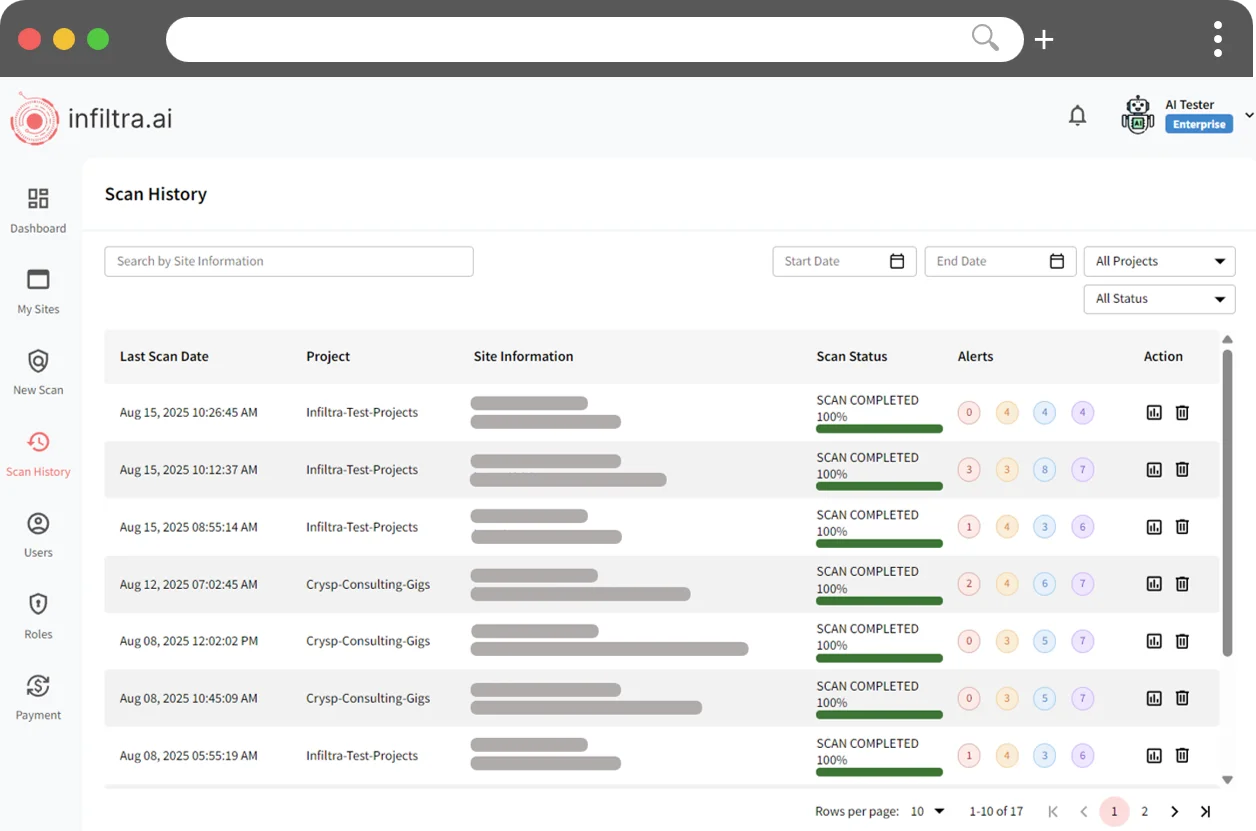
Retest prior findings against a selected full scan and produce delta-focused reporting.
Create roles mapped to Projects and Configs. Delegated users can only see assigned projects and reports.
CI/CD Hooks and APIs to pipeline Continuous Security Testing as part of your DevSecOps. Export vulnerability findings as JSON/CSV.
Aligns to OWASP Top 10 and SANS 25. Findings mapped and severity-scored with CVSS (0.0–10.0).
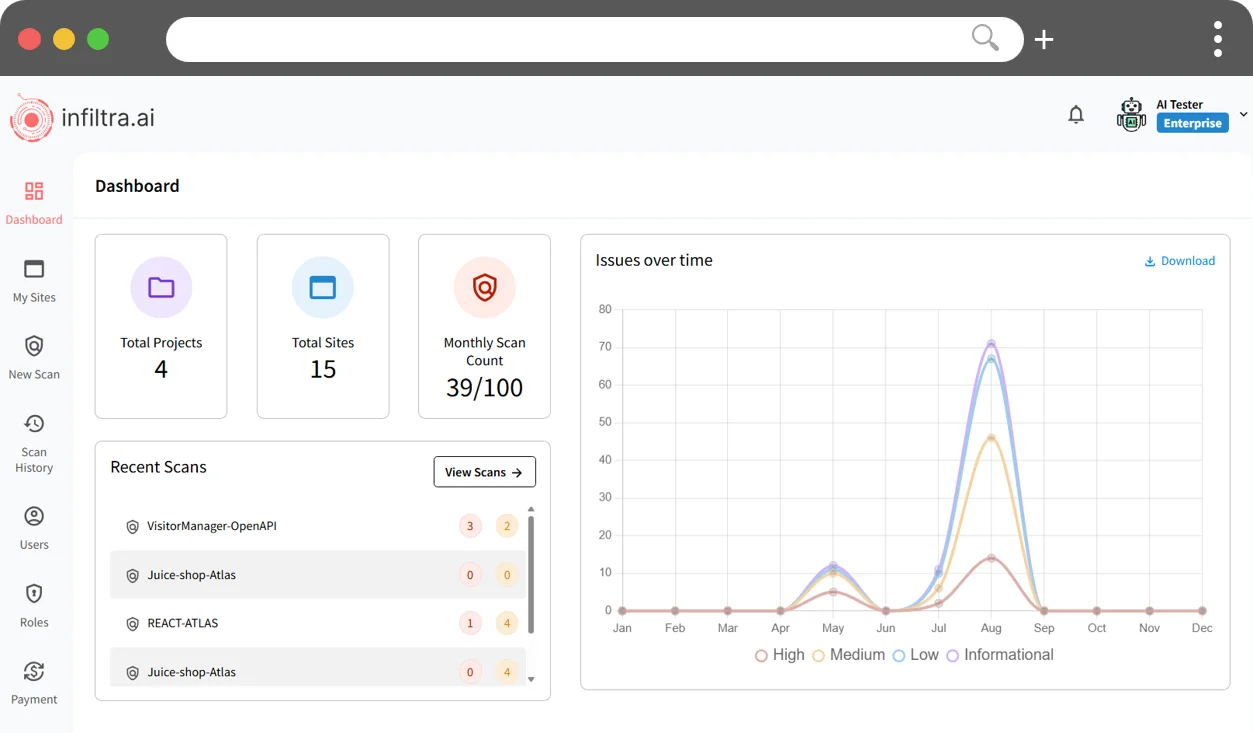
A unified dashboard for scan activity, validated findings, and remediation progress.
Infiltra was born out of real-world security problems we repeatedly saw during client engagements.
We saw that point-in-time assessments go stale quickly, findings are often noisy and lack validation.
Drawing on decades of senior leadership across engineering and consulting, we built Infiltra to deliver continuous, pentest-quality outcomes.
Operates out of San Francisco (HQ), Melbourne and India



Testimonials from teams using Infiltra.ai to ship faster with continuous assurance.

“Infiltra.ai has become a security extension to our app team, helping us stay ahead of emerging threats.”
“Infiltra.ai provides continuous, automated testing at a price point a startup can actually afford.”
Enterprise-grade safety and auditability—while keeping operations simple.
Each assessment runs in an isolated processor. After the scan is completed the processor destroyed and re-initialized to ensure no context is carried over for new scans.
Primary hosting in AWS Australia Region (Sydney) with US and EU residency options that can selected for individual scans.
Guardrails implemented to protect against runaway Agents and configurable request rate (RPS) to keep traffic within target load capacity.
New vulnerabilities don't wait for your next annual pentest.
Test
against your live environment now to uncover hidden gaps before attackers do.